Introduction
Greetings, intrepid explorers of the cryptographic universe! As we continue our voyage from the foundational shores of Zero-Knowledge Proofs (ZKPs), you’re about to embark on an expedition of epic proportions. Picture this as a thrilling sequel to our previous adventure, where we uncovered the mysteries of ZKPs. Today, we’re venturing into uncharted waters, immersing ourselves in the intricate landscapes of zkSNARKs and zkSTARKs. Brace yourselves for an exhilarating ride through finite fields, commitment schemes, and cryptographic proof systems. By journey’s end, you’ll wield the knowledge to demystify these enigmatic cryptographic tools and emerge as a true cryptography connoisseur. So, fasten your seatbelts and get ready to unlock the arcane secrets of zkSNARKs and zkSTARKs – your ticket to cryptographic mastery awaits!
What are zkSNARKs
zkSNARKs – Zero-Knowledge Succinct Non-Interactive Argument of Knowledge, as the acronym suggests, allow one party (the prover) to demonstrate knowledge of a certain computation or information to another party (the verifier) without disclosing the specifics of how that knowledge was acquired. These proofs are succinct, meaning they are compact and require minimal data to convey the validity of the computation. This property makes zkSNARKs particularly appealing for scaling blockchain computations and ensuring transaction privacy.
The Power of SNARKs in Scaling Blockchain Computation
Blockchain technology heavily relies on cryptographic proofs to ensure the integrity and validity of transactions. However, the computational burden of verifying each transaction on every full node can hamper scalability and lead to high network usage. zkSNARKs provide an elegant solution by enabling complex computations to be executed on powerful computers, while the verification process remains lightweight and efficient for nodes with limited computational resources. This allows for a significant boost in blockchain throughput without compromising security.
Primer to the world of creating a zkSNARK (Math Alert!)
We will embark on an exciting exploration of the basic mathematics behind designing a zkSNARK proof. Delving into concepts like finite fields, modular arithmetic, and computation arithmetization, we will demystify the inner workings of zkSNARK. So, get ready to dive into the world of zkSNARKs and understand the mathematical wizardry that underlies these powerful cryptographic tools.
Finite Fields
At the heart of zkSNARKs lies the concept of finite fields. These are finite sets of elements with specific arithmetic operations like addition, subtraction, multiplication, and division. One crucial characteristic of finite fields is their closed property, meaning that any operation on two elements within the field yields another element in the field. zkSNARKs operate on finite fields with prime order, wherein the number of elements (prime order) is a prime number or an order of prime raised to a power
Let’s try to understand about finite fields with an easy example…
Think of them as special secret agent playgrounds with a fixed number of elements. You can only play within this playground, and once you reach the end, you loop back to the beginning. Let’s use the finite field GF(11) as our example.
GF(11) Playground:
0, 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 0, 1, 2, …
In this playground, addition, subtraction, multiplication, and division work differently from regular math. For example, in GF(11), 6 + 7 is not 13, but instead wraps around to 2. It’s like a secret agent’s arithmetic! Let me crack this secret code for you, 6+7 = 13mod11 = 2 (13/11 with a remainder 2, tadaaa!)
Modular Arithmetic
Modular arithmetic is another fundamental concept. It ensures that calculations wrap around within the finite field, ensuring the results stay within the valid range of elements. When performing mathematical operations on field elements, they are expressed in the form of “result mod order” to remain within the field’s boundaries.
Alright, let’s put on our mathematical sunglasses and understand with a help of example…
Imagine you and your secret agent buddy Bob are exchanging messages in code. To make sure your messages are safe, you use modular arithmetic, which is like a secret agent clock with limited hours. Let’s use a simple clock with only 12 hours for our example.
On this cool clock, we call it “mod 12”, the numbers are 0 to 11, just like the hours of a regular clock.
Now, let’s do some cool spy math!
Addition: When you add two numbers on this clock, you go around the clock and stop at the remainder. For example, 8 + 7 is not 15 but 3 because you went around once and stopped at 3.
Subtraction: Subtraction works similarly. If you subtract 5 from 9, you don’t get -4, but you go around the clock and end up at 4.
Multiplication: When you multiply, you can still go around the clock. For instance, 3 * 4 is not 12, but 0 (just like finite fields, 12mod12) because you went around the clock once.
Division: Division is a bit trickier. You have to find a “secret agent number” (called the modular inverse) that, when multiplied with the original number, gives you 1. For example, the modular inverse of 3 in “mod 12” is 9 because 3 * 9 = 27, and when you go around the clock, you end up at 3 * 9 mod 12 = 3.
Arithmetization using Arithmetic Circuits
In this magical realm, zkSNARKs are the secret keepers and arithmetization is their spellbook.
Picture arithmetization as a powerful wand that transforms complex problems into elegant arithmetic circuits. These circuits, like magical charms, perform mathematical wonders using binary spells, all while safeguarding the mysteries they encode.
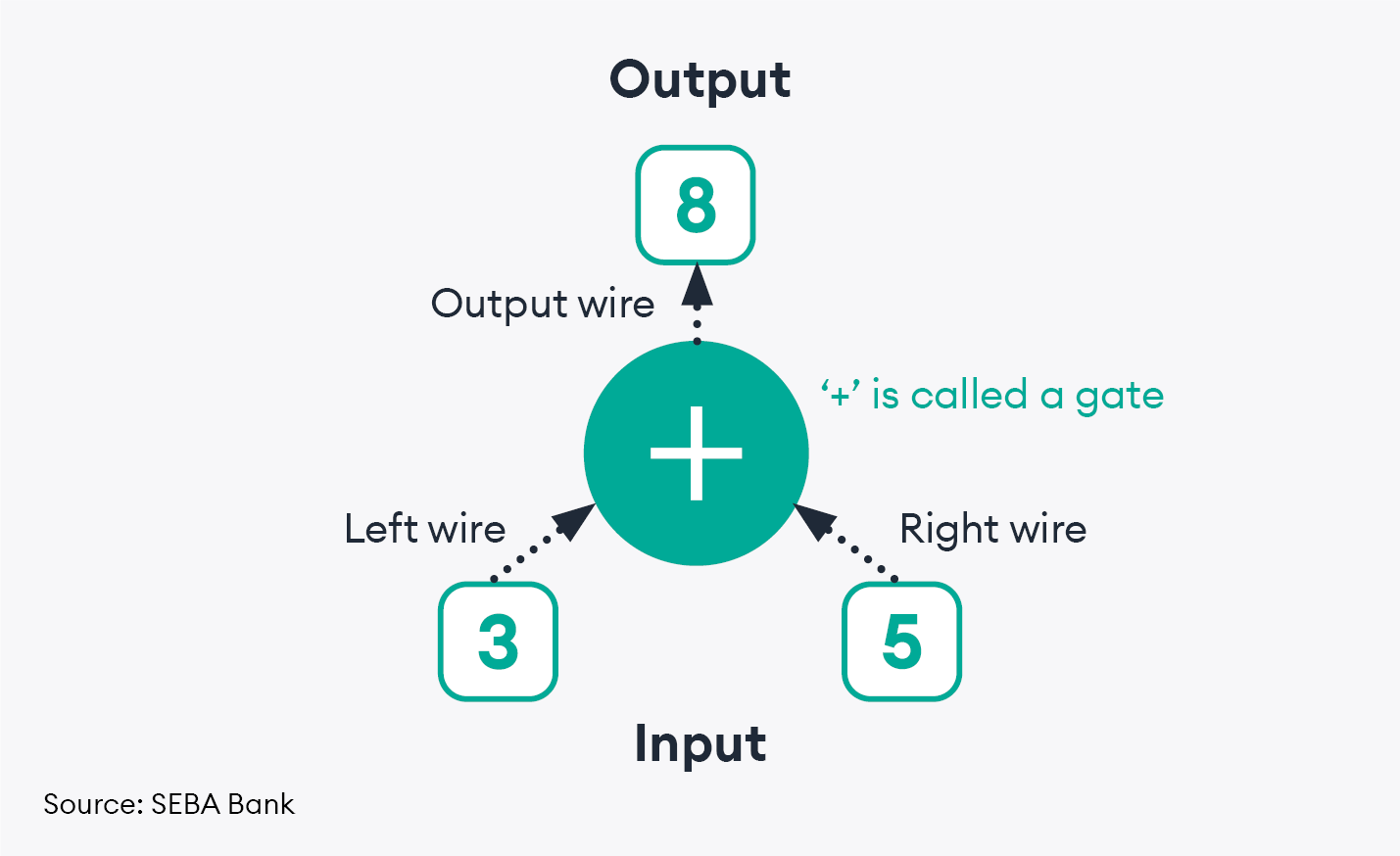
Arithmetization is like building a simple calculator with wires and components to perform basic math operations. Instead of using regular numbers, we represent them with electrical signals. For example, if we have the addition problem “3+5=8,” we can model this as:
Like the above circuit, larger circuits can represent larger order systems. The logical programs written to specify input, output and intermediate signals is then turned into arithmetic circuits.
Computational Process
Arithmetization is a powerful technique that takes a complex computational process described in a programming language and transforms it into a set of mathematical constraints. This transformation allows for efficient verification of the computation’s correctness using zkSNARK proofs and quadratic polynomials in the QAP format.
Let’s break down the process of arithmetization and how it goes from a circuit description to the final step of generating a Quadratic Arithmetic Program (QAP) through the Rank-1 Constraint System (R1CS).
Circuit Description: Arithmetization starts with a circuit description, which could be a computational process defined in a programming language. This circuit might involve various operations like additions, multiplications, and more complex computations.
Rank-1 Constraint System (R1CS): The first step in arithmetization is to convert the circuit into a Rank-1 Constraint System (R1CS). This involves transforming the circuit’s logical operations into a series of mathematical constraints. Each constraint asserts that the product of two vectors (representing inputs and intermediate variables) equals another vector (representing outputs). Mathematically, this can be written as
left * right = output, or equivalently, left * right – output = 0.
Benefits of R1CS: The R1CS representation allows for fast verification of computations. Instead of having to check each step of the computation, the verifier only needs to verify these algebraic constraints, which can significantly speed up the process.
Quadratic Arithmetic Program (QAP): The R1CS is then further transformed into a Quadratic Arithmetic Program (QAP). This involves representing the R1CS constraints as polynomials, specifically quadratic polynomials. The QAP format is used to efficiently generate Zero-Knowledge Succinct Non-Interactive Argument of Knowledge (zkSNARK) proofs.
Generating zkSNARK Proof: A prover can use the QAP to generate a zkSNARK proof that they know a valid witness (a set of values that satisfy the constraints), without revealing any specific information about the witness itself. This proof is generated using advanced cryptographic techniques.
Verification: The verifier can then take the zkSNARK proof and the QAP, and using a relatively small number of checks, verify the validity of the proof. The verification process involves checking the algebraic relationships between the polynomials representing the R1CS constraints.
Just definitions aren’t enough, right? Let’s take it up a notch for our understanding and explain the Rank-1 Constraint System (R1CS) with a simpler example involving a basic arithmetic circuit:
Imagine we have a simple arithmetic circuit with three input variables (in1, in2, and in3) and one output variable (out). The circuit computes the output as follows: out = (in1 + in2) * in3.
We want to convert this circuit into R1CS format to enable efficient verification.
Step 1: Flattening the Circuit
We represent the circuit as a series of mathematical constraints:
Constraint 1: in1 + in2 – tmp1 = 0
Constraint 2: tmp1 * in3 – out = 0
Here, tmp1 is an intermediate variable introduced to capture the result of (in1 + in2) before it’s multiplied by in3.
Step 2: Labeling Wires and Gates
We label the wires and gates as follows:
Inputs: in1, in2, in3
Outputs: out
Intermediate Variable: tmp1
Gates: g1 (corresponding to Constraint 1), g2 (corresponding to Constraint 2)
Step 3: Create the R1CS
For each gate, we form the left, right, and output vectors to construct the R1CS equations:
Gate g1:
left: [1, 1, 0, 0] (coefficient of in1, in2, tmp1, and out in Constraint 1)
right: [in1, in2, 0, 0] (values of in1, in2, tmp1, and out in Constraint 1)
output: [0, 0, 1, 0] (values of in1, in2, tmp1, and out in Constraint 1)
Gate g2:
left: [0, 0, 1, 0] (coefficient of in1, in2, tmp1, and out in Constraint 2)
right: [0, 0, in3, 0] (values of in1, in2, tmp1, and out in Constraint 2)
output: [0, 0, 0, 1] (values of in1, in2, tmp1, and out in Constraint 2)
Step 4: Prover’s Witness
Let’s assume the prover knows the values of in1=3, in2=2, in3=4 (random values for illustration).
The prover constructs the witness vector:
Witness (w) = [1, 3, 2, 4]
Step 5: Generating Matrices
Using the witness and the R1CS equations, we create the left, right, and output matrices for each gate.
Gate g1:
left matrix: [[1, 1, 0, 0], [0, 0, 0, 0], [0, 0, 0, 0], [0, 0, 0, 0]]
right matrix: [[3, 2, 0, 0], [0, 0, 0, 0], [0, 0, 0, 0], [0, 0, 0, 0]]
output matrix: [[0, 0, 1, 0], [0, 0, 0, 0], [0, 0, 0, 0], [0, 0, 0, 0]]
Gate g2:
left matrix: [[0, 0, 1, 0], [0, 0, 0, 0], [0, 0, 0, 0], [0, 0, 0, 0]]
right matrix: [[0, 0, 0, 4], [0, 0, 0, 0], [0, 0, 0, 0], [0, 0, 0, 0]]
output matrix: [[0, 0, 0, 0], [0, 0, 0, 0], [0, 0, 0, 1], [0, 0, 0, 0]]
Finally, with these vectors and the witness ‘w,’ we can express the original computation was performed with one of the input variables [3,2,4] and pass this into the proving system than can generate the SNARK proof.
There are many other arithmetization techniques to use in addition to R1CS and QAP, such as Boolean Arithmetization, Arithmetic Intermediate Representation (AIR), Elliptic Curve Arithmetization etc. Don’t worry! we will not delve into these techniques today, may be some other time!
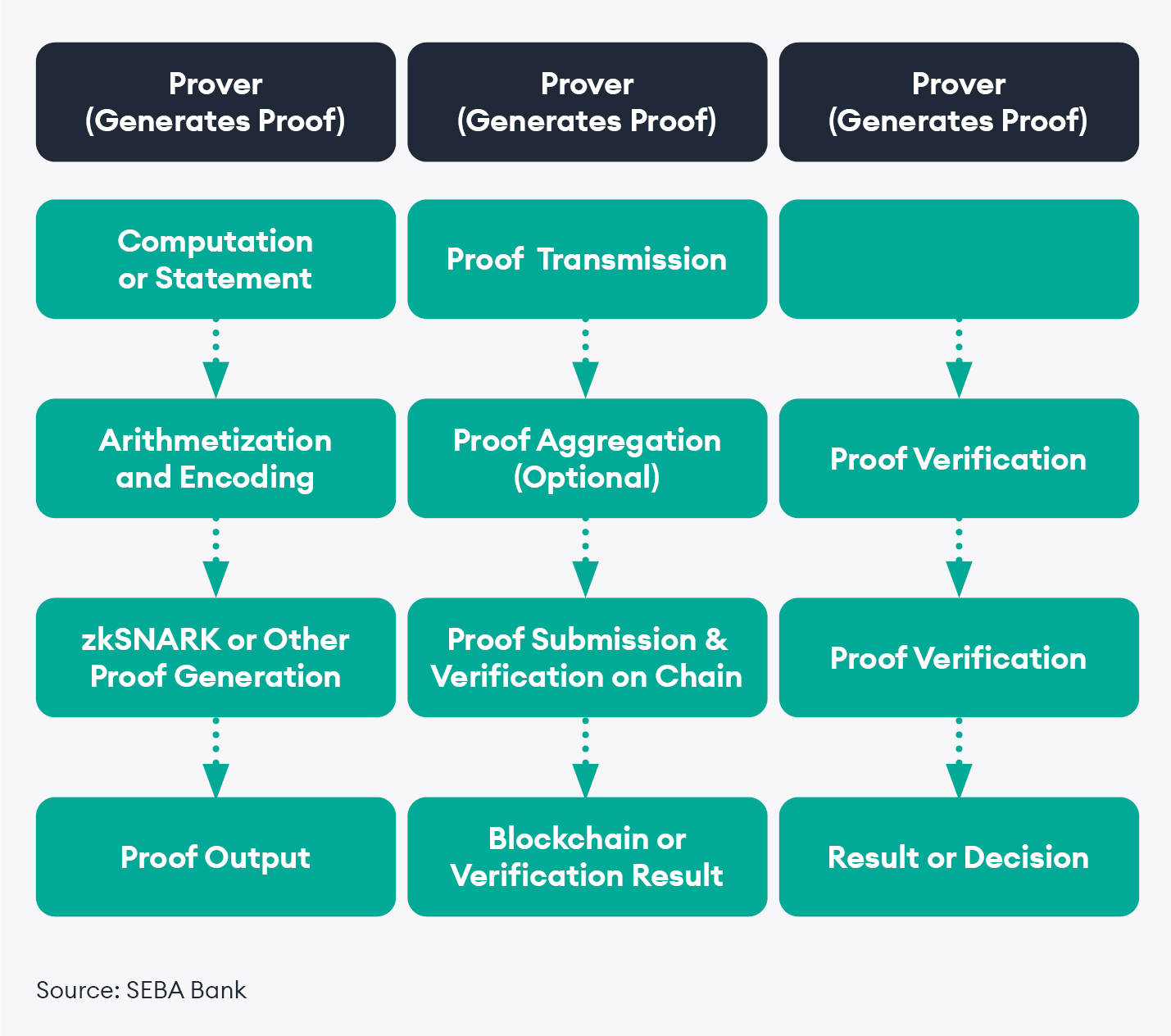
Crypto is hard, explaining it is harder! But I try to keep make things simple just like a lazy person! Below, I have tried to give a simple yet detailed schematic representation of how the different components works together to enable the generation, transmission, and verification of the cryptographic proof system.
For today’s discussion we are focused only on the left most column of the above diagram. Out of which I have tried to give you a glimpse of how starting from computation to constraints satisfaction problems are generated via arithmetization. Now, I will try to explain how last two components, Proof generation and Proof output, works and what happens in between these two steps. You will learn about commitment schemes, Interactive oracle proofs and cryptographic proof systems. One-stop shop! Isn’t it?!
Commitment schemes
In a Zero-Knowledge Proof (ZKP) context, commitment schemes are cryptographic techniques used to prove the existence of a value or statement without revealing the actual value itself. They play a vital role in maintaining privacy and security during interactive protocols. A commitment scheme involves creating a commitment to a value, which can be verified later without exposing the value.
I always believe in examples to solidify the understanding at the root level. Here you with another simple example to help you lock in what exactly is a commitment scheme:
Let’s say your secret message is a number, 7. You put 7 in the locked box. You give your friend the locked box and the magic number, let’s call it 5. Your friend calculates 5 * 7 = 35 and tells you the result. On your side, you also calculate 5 * 7 = 35. When you compare the results, they’re the same!
You’ve just proven that you have the number 7 inside the locked box, and your friend still doesn’t know what the number is. That’s a commitment scheme in action – a way to prove things without revealing your secrets.
The Famous scheme
One of the famous commitment schemes used to create Zero-Knowledge Proofs (ZKPs) is the KZG (Kate-Zaverucha-Goldberg) commitment scheme. KZG commitment scheme is based on polynomial interpolation and evaluation techniques, and it’s particularly efficient and secure when dealing with large-scale commitments.
In the KZG commitment scheme:
Polynomial Commitment: KZG commitments are based on polynomials. The prover commits to a polynomial by sending a constant-size commitment, which is like a succinct summary of the polynomial.
Polynomial Evaluation: The verifier can request the prover to evaluate the polynomial at specific points. The prover provides these evaluations without revealing the polynomial itself.
Homomorphic Properties: One of the key strengths of KZG commitments is their homomorphic properties. This means that you can combine commitments to different polynomials to get a commitment to their sum or product, without revealing the individual polynomials.
Verification: Verifying KZG commitments is efficient. The verifier can use these commitments to check that the polynomial evaluations match the claimed values without needing to know the polynomials themselves.
Opening the Commitment: When necessary, the prover can reveal the original polynomial and its evaluations at chosen points. This helps prove the correctness of a computation without revealing the full polynomial.
After arithmetization transforms a computation into mathematical constraints and a commitment scheme hides the computation’s details, Interactive Oracle Proofs (IOPs) step in as the clever communication strategy. Imagine you and your friend are solving a puzzle together. Arithmetization is like breaking the puzzle into small pieces, and the commitment scheme locks each piece in a box. Now, IOPs let you and your friend chat in code – your friend asks tricky questions about parts of the puzzle, and you provide smart answers without exposing everything. These back-and-forth interactions let your friend become a puzzle-checker wizard, confirming that your commitment scheme and arithmetization are spot on. It’s like teamwork where your secret code language convinces your friend that the puzzle is solved while keeping your secrets safe!
Interactive Oracle Proofs (IOPs)
Interactive oracle proofs (IOPs) are a cryptographic protocol used to efficiently prove the validity of a computation or a statement while minimizing the amount of communication required between the prover and the verifier. In an IOP, the prover and verifier engage in a series of interactions where the verifier acts as an oracle, posing random queries to the prover, who responds with information derived from the computation’s witness.
The key idea behind IOPs is to divide the computation into smaller sub-computations, which are organized in a binary tree structure. The prover and verifier then interact to verify each sub-computation independently. This allows the verifier to make random queries about specific parts of the computation without having to understand the entire computation.
Cryptographic Proof Systems
After the Interactive Oracle Proofs (IOP) process, cryptographic proof systems like Plonk step in to create strong and efficient proofs for various applications. Imagine you and your friend solved a puzzle using IOPs, where you answered their tricky questions about your solution. Now, you want to prove to others that you solved the puzzle correctly without revealing the solution. Cryptographic proof systems, like Plonk, create succinct proofs that confirm your puzzle-solving skills. These proofs can be easily verified by others to ensure the accuracy of your claim without needing to understand the puzzle itself.
Here are four examples of cryptographic proof systems:
Groth16: Groth16 is a proof system that’s great for privacy-focused blockchain applications like Zcash. It generates short proofs that can be quickly verified, enabling transactions to be validated without revealing transaction details.
Bulletproofs: Bulletproofs are another proof system known for their efficiency. They’re used to verify statements about committed values while keeping proofs small. Bulletproofs are employed in Monero to ensure the confidentiality of transaction amounts.
Halo: Halo is a recent proof system that enables recursive proofs, allowing you to prove the validity of multiple proofs within a single proof. This efficiency improvement is valuable in blockchains and other applications where complex proofs need to be verified.
Plonk: Plonk is another advanced zero-knowledge proof system that stands for “Permutations over Lagrange-bases for Oecumenical Noninteractive arguments of Knowledge.” Plonk aims to provide high efficiency and versatility in proof generation and verification. It’s designed to be especially efficient for a wide range of computations and is used in various decentralized applications, including blockchains. Plonk is praised for its ability to handle complex computations while keeping proof sizes small and verification times fast.
ZK-STARK
Before moving ahead with zkSTARK, I have a message so that you don’t get disappointed when delving further ahead in the article. Here it goes:
“In our journey through the enchanted realm of cryptography, we’ve already embarked on a thrilling expedition into the realm of zkSNARKs. We’ve bravely deciphered mathematical spells that let us prove the truth of statements without revealing any sensitive details. But, as the horizon broadens, we stumble upon the looming silhouette of zkSTARKs, another enigmatic facet of this arcane world.
However, dear adventurers, brace yourselves, for the land of zkSTARKs is lush with even deeper layers of mathematical magic. As captivating as it may be, venturing into zkSTARK mathematics within the same scroll would be akin to unlocking a treasure chest brimming with knowledge gems. In our quest to strike a balance between enlightenment and comprehension, we’ll temporarily withhold these intricate incantations for a future saga.
Rest assured, intrepid seekers of knowledge, the day shall come when we delve into the wondrous depths of zkSTARKs, uncovering their mathematical underpinnings with a blend of clarity and wonder. Until then, our focus remains steadfast on illuminating the secrets of cryptography one enchanted step at a time.
And
Congratulations, dear readers, for journeying alongside us this far into the cryptic realms of knowledge. Your curiosity and dedication are the true magic that fuels our exploration. Here’s to your insatiable thirst for wisdom and your unyielding spirit in unraveling the mysteries of cryptography. Keep shining brightly as the beacons of enlightenment! Cheers to you all!”
What is zkSTARK?
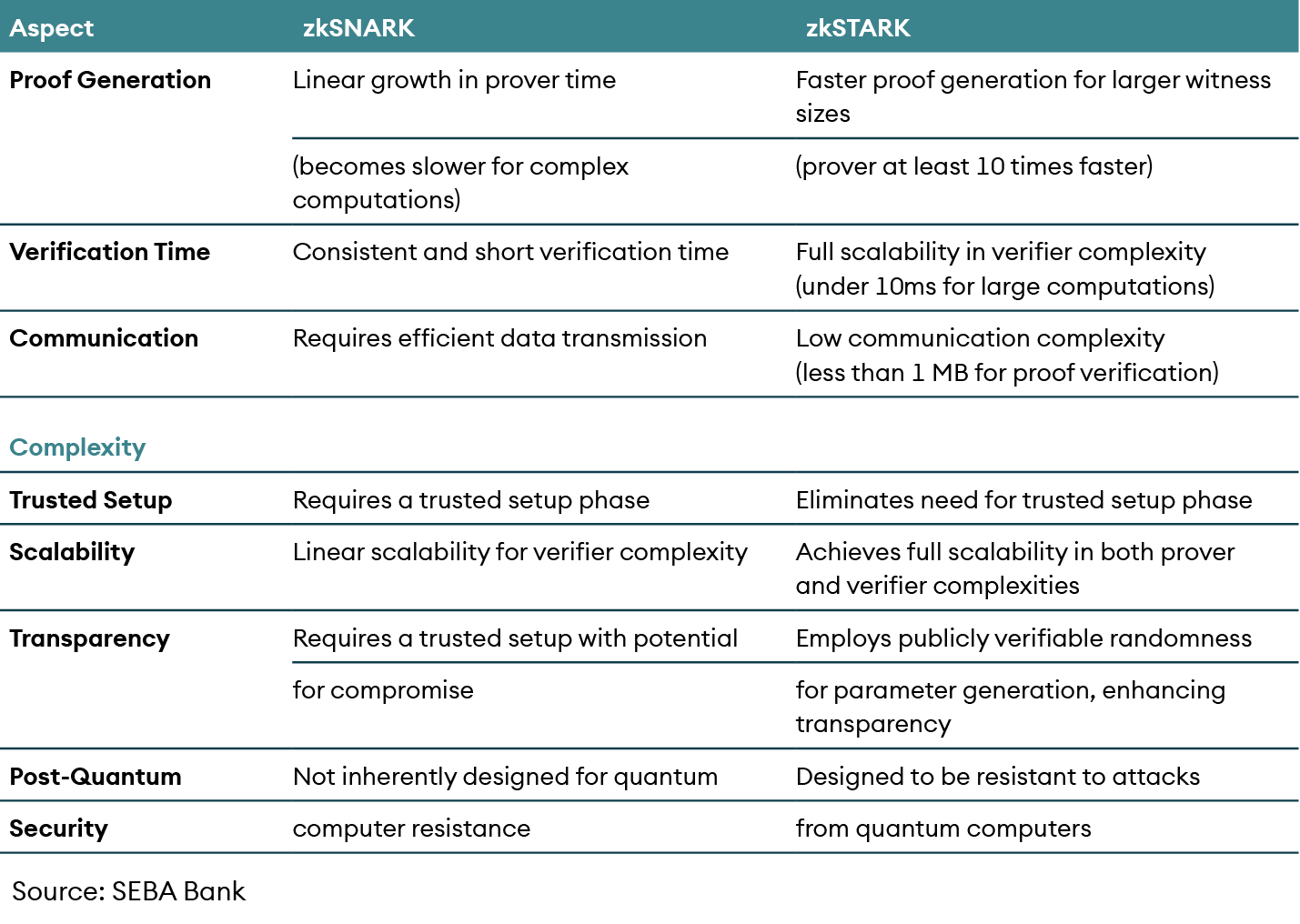
ZK-STARK is an acronym for Zero-Knowledge Scalable Transparent Argument of Knowledge. ZK-STARKs are similar to ZK-SNARKs, except that they offer distinct advantages:
Scalable: ZK-STARKs exhibit faster proof generation and verification for larger witness sizes. While ZK-SNARKs show linear growth in prover and verifier times, STARKs maintain efficiency even as the witness size increases.
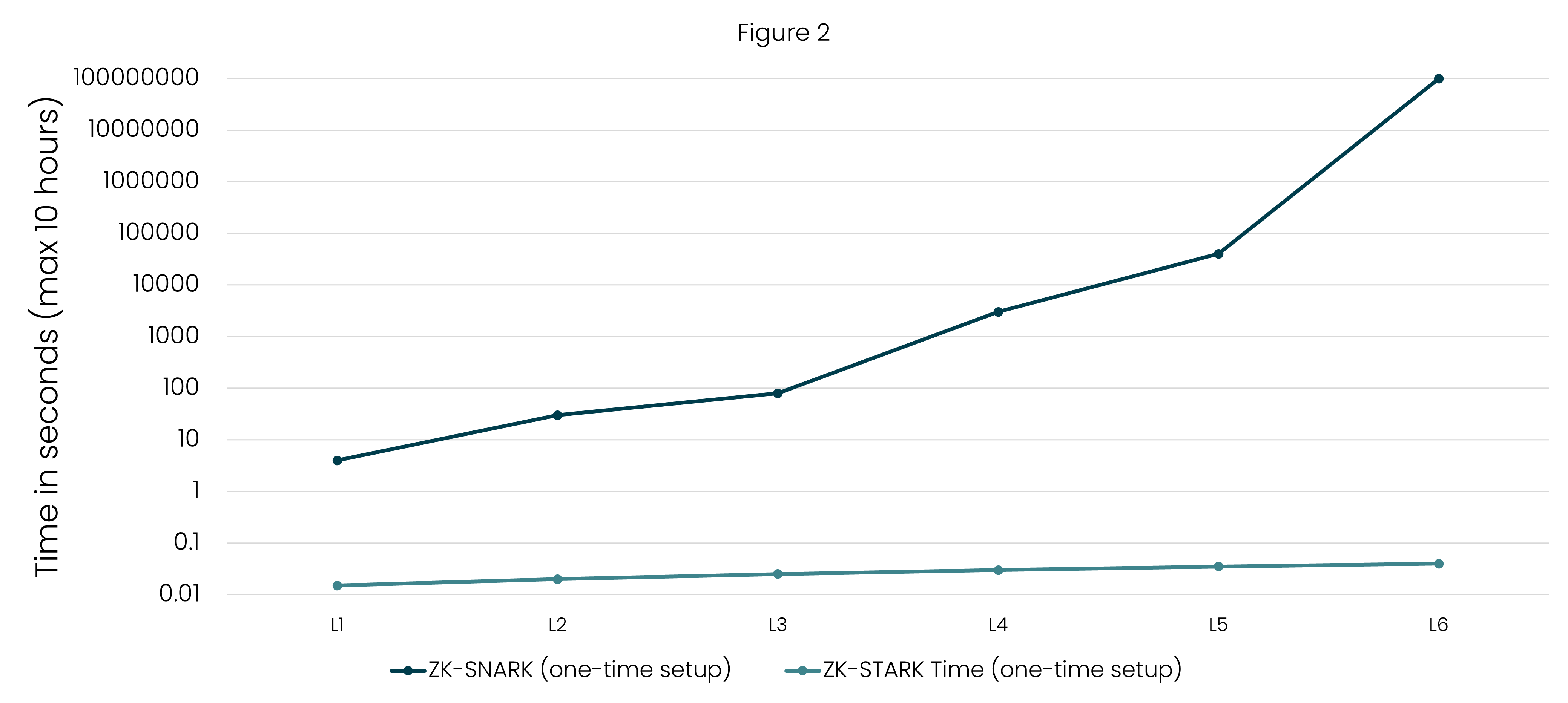
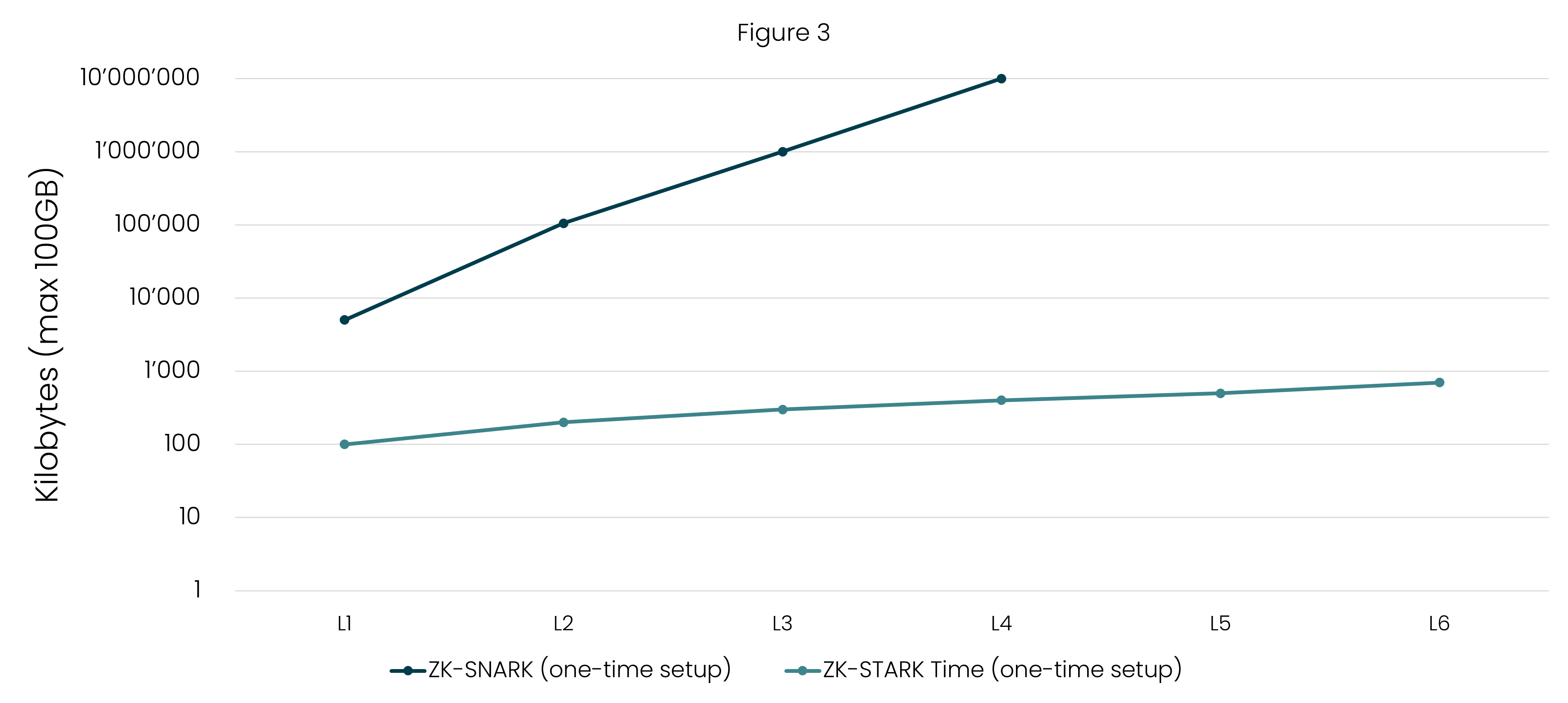
Transparent: Unlike ZK-SNARKs that require a trusted setup, ZK-STARKs employ publicly verifiable randomness for generating public parameters, enhancing transparency, and reducing reliance on centralization.
Post-Quantum Security: zkSTARKs are designed to be resistant to attacks from quantum computers, which have the potential to break some cryptographic schemes, including those used in zkSNARKs. zkSTARKs provide a more robust defense against the threat of quantum computing advancements.
Transparency: Trusted setup phase
In zkSNARK, the trusted setup phase is a critical step that lays the foundation for the entire system. During this phase, a group of participants generates and shares cryptographic parameters, which are used to create and verify proofs. These parameters include proving and verifying keys that must be kept secret to prevent attacks. However, the need to generate and distribute these keys raises concerns. If even a single participant is malicious or compromised, they could create fake proofs or compromise the entire system’s security.
In contrast, zkSTARK eliminates the need for a trusted setup phase. This is achieved by leveraging publicly verifiable randomness to create the parameters used in the proof system. The absence of a trusted setup phase in zkSTARK makes the system more transparent and eliminates the risk associated with compromised participants. This is a significant advantage, as it ensures that the security of the system is not dependent on a handful of participants maintaining secrecy and honesty during the setup process.
Scalability
To fully grasp the scalability of zk-STARK, it’s essential to delve into three critical aspects: prover complexity, verifier complexity, and communication complexity. In addition to other aspects, these dimensions collectively determine the efficiency and speed of zk-STARK’s operation.
In the context of cryptographic proof systems like ZK-STARK, the terms “prover complexity,” “verifier complexity,” and “communication complexity” refer to different aspects of the computational resources required to generate and verify proofs. Let’s break down these concepts:
Prover Complexity
Prover complexity refers to the computational resources and time required for the prover to generate a proof. In the whitepaper, it’s mentioned that the ZK-STARK prover is at least 10 times faster than other measured systems across various computation sizes. For example, let’s consider a computation with a certain number of gates, say n = 2^15 (32,768). The ZK-STARK prover can generate a proof for this computation in around 100 milliseconds. This speed advantage holds true for a range of computation sizes.
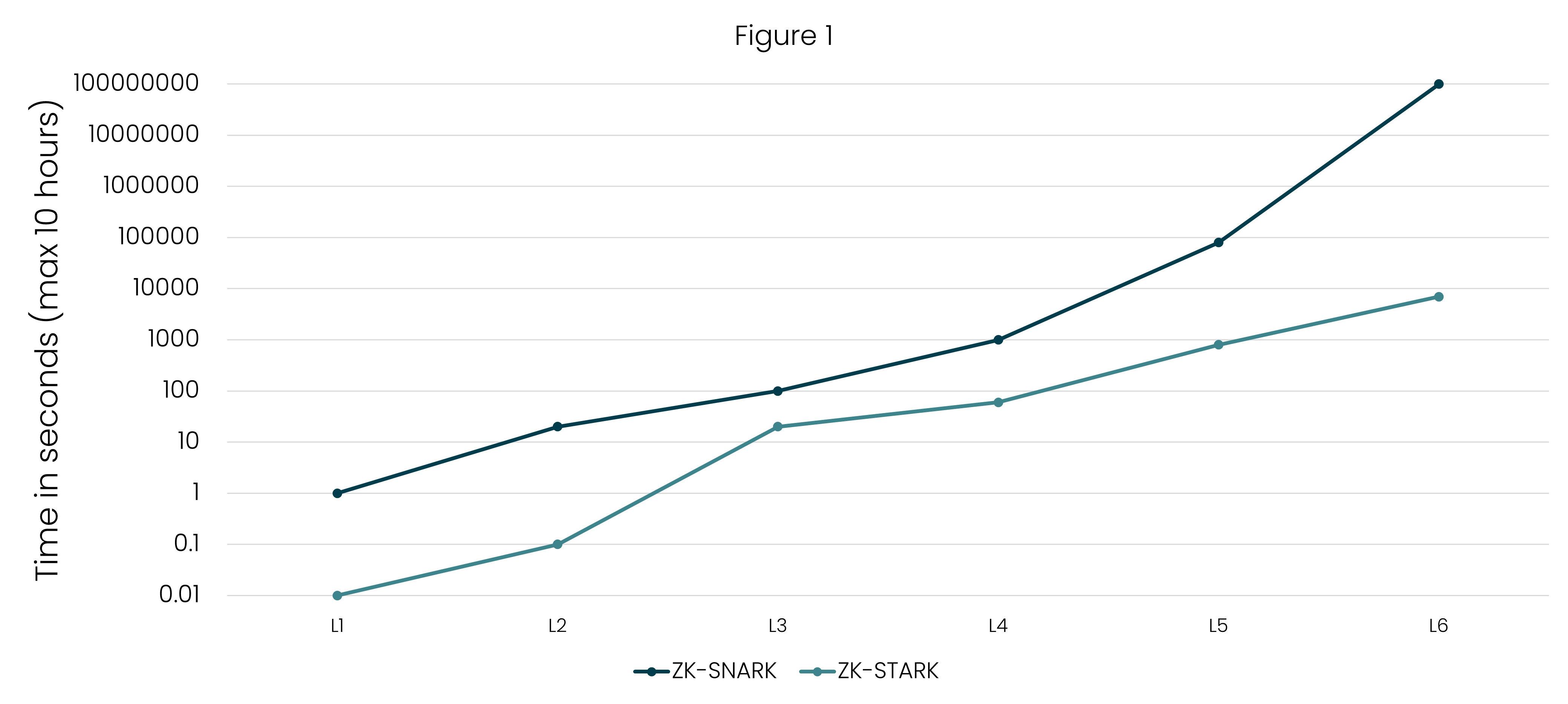
Verifier Complexity
Verifier complexity refers to the computational resources and time required for the verifier to verify the proof generated by the prover. The whitepaper highlights that ZK-STARK achieves full scalability in terms of verifier complexity. For a computation size similar to the one above (n = 2^15), the verification time for ZK-STARK is under 10 milliseconds. This means that the time it takes to verify the proof is very short and remains consistent even as the computation becomes more complex.
Communication Complexity
Communication complexity refers to the amount of data exchanged between the prover and the verifier during proof verification. ZK-STARK is designed to have low communication complexity. For instance, the amount of data transmitted during proof verification, even for large computations, is less than 1 megabyte (MB). This efficient communication helps maintain fast verification and reduces the burden on the network.
Quantum Computing
Quantum computing is a paradigm of computing that exploits the principles of quantum mechanics to process information in ways that classical computers cannot. Classical computers use bits to represent information as either 0 or 1, while quantum computers use qubits, which can exist in a superposition of states, enabling them to represent both 0 and 1 simultaneously. This property allows quantum computers to perform certain types of calculations exponentially faster than classical computers. Quantum computers also benefit from entanglement, a phenomenon where qubits become correlated in ways that classical bits cannot.
Why Bitcoin and Ethereum are vulnerable to attacks in future and what is the solution?
Quantum computers have the potential to break certain cryptographic algorithms that are widely used for securing digital transactions, data privacy, and more. Two popular cryptocurrencies, Bitcoin and Ethereum, rely on the ECDSA (Elliptic Curve Digital Signature Algorithm) for digital signatures and security. Here’s a brief overview of how quantum computers could impact Bitcoin and Ethereum, and how transitioning to other algorithms like lattice-based or multivariate-based cryptography could address these concerns:
Bitcoin
Bitcoin uses the ECDSA algorithm to generate digital signatures for transactions, ensuring the authenticity and integrity of the transactions. Quantum computers with sufficient computing power could use Shor’s algorithm to efficiently factor large numbers, which could compromise the private keys associated with Bitcoin addresses. This means that a quantum computer could potentially generate the private key from a public key, allowing unauthorized access to Bitcoin funds.
Transition to Lattice-Based Cryptography:
Lattice-based cryptography is considered a promising candidate for post-quantum security. Lattice problems are believed to be hard for both classical and quantum computers to solve efficiently. By transitioning to a lattice-based cryptographic scheme, Bitcoin could ensure its security even in the presence of powerful quantum computers.
Ethereum
Similar to Bitcoin, Ethereum also relies on the ECDSA algorithm for digital signatures and authentication. If quantum computers become capable of breaking ECDSA, Ethereum transactions and smart contracts could be vulnerable to unauthorized access and manipulation.
Transition to Multivariate-Based Cryptography:
Multivariate-based cryptography is another post-quantum alternative. By using systems of multivariate polynomial equations, such cryptography resists quantum attacks. Ethereum could potentially transition to a multivariate-based cryptographic scheme to ensure its security against quantum threats.
In both cases, transitioning to post-quantum cryptographic algorithms involves challenges and considerations. New algorithms need to be carefully evaluated for their security, efficiency, and compatibility with existing systems. Additionally, the transition may require changes to the underlying protocols and software implementations.
Overall, the threat posed by quantum computers to the security of ECDSA-based systems like Bitcoin and Ethereum highlights the importance of preparing for the post-quantum era. As quantum computing advances, the cryptocurrency community needs to explore and adopt cryptographic solutions that remain secure even in the face of quantum attacks.
Why ZK-STARK is resistant to quantum computing?
Quantum computers have the potential to solve complex mathematical problems, such as factoring large numbers, way faster than classical computers. This could jeopardize the security of many cryptographic protocols, including those that underpin zkSNARKs.
However, zkSTARKs utilize cryptographic techniques that are resistant to quantum computing due to the cryptographic techniques they employ, which are based on mathematical problems that are believed to be hard for quantum computers to solve efficiently. This resistance can be understood through a few key aspects:
Mathematical Complexity: zkSTARKs rely on mathematical problems, such as polynomial interpolation and evaluation, that don’t have known efficient quantum algorithms to break them. Quantum computers are exceptionally fast at solving certain types of problems, but these problems are different from the ones zkSTARKs rely on. As a result, zkSTARKs remain secure against quantum attacks.
Algebraic Structures: zkSTARKs utilize algebraic structures like finite fields and mathematical operations that aren’t easily exploited by quantum speedup. Quantum computers can’t efficiently exploit these structures to undermine the security of zkSTARKs.
Quantum Grover’s Algorithm: Quantum computers can use Grover’s algorithm to speed up searches in an unsorted database quadratically. This algorithm can undermine certain classical cryptographic schemes, like brute-forcing passwords or encryption keys. However, zkSTARKs are designed to be resistant to Grover’s algorithm. The zkSTARK construction ensures that the quantum speedup provided by Grover’s algorithm does not compromise the security of the proofs generated.
In summary, zkSTARKs resist quantum attacks by relying on mathematical problems and algebraic structures that quantum computers can’t easily exploit. This resistance makes zkSTARKs a viable cryptographic solution even in the face of advancements in quantum computing, ensuring the security and privacy of digital transactions and computations.
One Stop Comparison ZK-SNARK vs ZK-STARK (The AMINA way!)
Use cases of Zero-Knowledge Proofs (ZKPs)
Zero-knowledge proofs (ZKPs) have a wide range of use cases across various industries and applications due to their ability to provide secure and private validation of information without revealing sensitive data. Here are some notable use cases of zero-knowledge proofs:
Blockchain and Cryptocurrencies: ZKPs are widely used in blockchain networks to ensure transaction privacy and data integrity. They allow users to prove ownership of specific assets or verify transactions without revealing sender/receiver information or transaction amounts. Examples include Monero’s use of ZKPs for transaction amounts and Zcash’s use for shielded transactions.
Authentication and Identity: ZKPs can be used for secure and private authentication processes. Users can prove their identity or access rights without disclosing personal information, reducing the risk of data breaches or identity theft.
Data Sharing and Privacy: ZKPs enable data sharing while preserving privacy. Businesses can prove the accuracy of their data without revealing actual values, which is valuable in scenarios like compliance audits or sharing medical records.
Digital Voting: ZKPs can be applied in secure voting systems to ensure voter anonymity and the integrity of election results. Voters can prove that their vote was counted correctly without revealing their choice.
Supply Chain Tracking: ZKPs can help in verifying the authenticity and origin of products in supply chains without exposing sensitive business information. This is useful in preventing counterfeiting and ensuring product quality.
Smart Contracts: In blockchain-based smart contracts, ZKPs can be used to verify the fulfillment of contract terms without revealing the contract details to external parties.
Password-Free Authentication: ZKPs can enable password-free authentication by proving knowledge of a secret without disclosing the actual secret, enhancing security while simplifying user experience.
Healthcare: ZKPs can allow medical researchers to analyze sensitive patient data without violating patient privacy. This is crucial for medical breakthroughs while complying with data protection regulations.
Digital Signatures: ZKPs can enhance digital signatures by proving that a digital document was signed by a particular entity without revealing the actual content of the document.
Verifiable Credentials: ZKPs can be used to issue and verify credentials such as diplomas, certifications, and licenses without revealing unnecessary personal information.
Cloud Computing: ZKPs can enable secure computation on encrypted data in cloud environments, allowing users to perform calculations on sensitive data without exposing the data itself.
Cybersecurity: ZKPs can enhance security protocols by allowing parties to prove their identity or credentials without revealing sensitive information to potential attackers.
Conclusion
In the captivating world of cryptography, we’ve unveiled the magic of zkSNARKs and zkSTARKs. These cryptographic wonders empower us to prove truths without revealing their essence, offering scalability, privacy, and quantum resilience. From finite fields to commitment schemes, our journey through arithmetization and cryptographic proof systems has been a dance of elegance and security. As we embrace the promise of zkSTARKs’ transparency and quantum immunity, we salute your insatiable curiosity that lights our path through the enchanting realm of knowledge.
But this is only the beginning. As the guide through this arcane landscape, I’m dedicated to unraveling complexities and presenting them with clarity. The world of crypto can be complex, but my mission is to make it simple. Stay tuned for more captivating insights, as we continue to explore the uncharted realms of cryptography together. Your curiosity fuels this journey, and the best is yet to come.